Business
KiloLimits: Comprehensive Guide to Data Caps

The Fundamentals of Bandwidth Management
In the modern digital era, the management of data flow is a critical component of network stability. As more devices connect to global infrastructures, service providers must implement various strategies to ensure that bandwidth is distributed fairly and efficiently. One such concept used in the technical measurement of these thresholds is kilolimits, which helps define the boundaries of data consumption for specific user groups. By setting these parameters, network administrators can prevent a single user from monopolizing the available resources, thereby maintaining a consistent speed for all participants on the local or wide area network.
Understanding these boundaries requires a look into how data is measured and throttled. Most consumers are familiar with gigabytes or terabytes, but at the architectural level, much smaller units are often used to fine-tune the delivery of packets. When a system reaches its predefined kilolimits, the network may respond by lowering the priority of that specific connection or reducing the overall throughput. This practice, often referred to as fair usage policy, ensures that the infrastructure does not become overwhelmed during peak hours. As we transition into a more data-heavy society with 8K streaming and cloud gaming, the precision of these management tools becomes increasingly vital for maintaining the integrity of the internet.
Technical Constraints in Modern Infrastructure
The physical hardware that powers our digital world has finite capabilities. Every fiber optic cable, router, and switch has a maximum capacity for how much information it can process at any given millisecond. To avoid hardware fatigue and systemic crashes, engineers design software protocols that act as governors. These protocols monitor the usage rates against kilolimits to ensure that the hardware operates within its safe thermal and electrical zones. This is especially important in mobile networks, where spectrum availability is limited and must be shared among thousands of users simultaneously.
When these technical thresholds are met, the system undergoes a process known as traffic shaping. This isn’t just about slowing things down; it’s about prioritizing essential data—like a Voice over IP call or a security update—over less critical traffic like a background video download. By adhering to these strict internal guidelines, providers can offer a more reliable service even under heavy load. The evolution of hardware has allowed these caps to rise significantly over the last decade, yet the principle of setting a ceiling remains a fundamental necessity in the world of telecommunications and server management.
Impact on Consumer Data Habits
For the average user, the existence of data ceilings often dictates how they interact with their devices. Whether it is choosing to download large files only when connected to a specific network or adjusting video quality to save on consumption, the presence of kilolimits shapes our digital behavior. Users who are aware of their specific thresholds are less likely to experience the frustration of a throttled connection or unexpected overage charges. This awareness has led to the development of numerous third-party apps and built-in system tools that help individuals track their usage in real-time.
As remote work and digital education become the norm, the demand for higher ceilings has never been greater. Families with multiple members on video calls simultaneously can quickly approach their allocated data amounts if they are not careful. Consequently, there is a growing movement toward “unlimited” plans, though even these often contain hidden “soft” caps that function similarly to traditional measurement units. Understanding the fine print of a service agreement allows consumers to choose the plan that best fits their lifestyle, ensuring they have the bandwidth they need for work, play, and everything in between without hitting an invisible wall.
Evolutionary Trends in Cloud Computing
Cloud storage and computing have revolutionized how businesses operate, but they have also introduced new complexities in data management. When a company moves its entire operation to a remote server, every action—from opening a document to running a complex simulation—contributes to the total data transit. Professional cloud providers use kilolimits to structure their pricing tiers, allowing businesses to pay for exactly what they use. This “pay-as-you-go” model is highly efficient but requires a deep understanding of data transit costs to avoid budget overruns.
The future of the cloud is leaning toward “edge computing,” where data is processed closer to the user to reduce the need for long-distance transit. This shift helps minimize the strain on the central network and allows for faster response times. By optimizing how data is moved and stored, providers can offer higher performance while maintaining the same cost-effectiveness. As artificial intelligence and machine learning continue to demand massive datasets for training, the methods used to track and limit data flow will need to become even more sophisticated to keep up with the exponential growth of the digital economy.
Security Protocols and Traffic Monitoring
From a cybersecurity perspective, monitoring data spikes is one of the most effective ways to identify a potential breach or a Distributed Denial of Service (DDoS) attack. Security systems are programmed to flag any connection that suddenly exceeds its usual kilolimits, as this could indicate that data is being exfiltrated by an unauthorized party. By setting baseline usage patterns, administrators can create an “early warning system” that detects anomalies before they turn into full-scale security incidents.
Furthermore, these limits play a role in preventing the spread of malware. Some types of malicious software are designed to turn a compromised computer into a “bot” that sends out thousands of spam emails or participates in network attacks. By having strict outbound data caps at the router or ISP level, the damage these bots can do is significantly mitigated. Security is not just about firewalls and passwords; it is about understanding the flow of information and ensuring that it remains within expected, healthy parameters. Constant vigilance over data metrics is a cornerstone of modern digital defense strategies.
The Role of Regulatory Bodies in Connectivity
Governments and regulatory agencies play a major role in how data limits are implemented and advertised to the public. In many regions, there are laws that prevent service providers from using kilolimits in a way that is deceptive or anti-competitive. For example, “Net Neutrality” debates often center on whether a provider should be allowed to throttle certain types of content while letting others pass through at full speed. Regulators ensure that the metrics used to measure data are transparent and that consumers are not being unfairly penalized for normal usage.
These agencies also work to bridge the “digital divide” by encouraging the deployment of high-speed infrastructure in rural or underserved areas. In these locations, the implementation of data caps can be even more contentious, as users may have only one provider and limited options for high-capacity plans. By setting standards for what constitutes “high-speed” and “fair usage,” regulators help ensure that access to the internet remains an equitable resource. The balance between a provider’s need to manage their network and a citizen’s right to access information is a delicate one that requires constant oversight and legal refinement.
Future Prospects for High-Speed Data
As we look toward the horizon of 6G and satellite-based internet constellations, the way we perceive and measure data is likely to change. The kilolimits of today may become the negligible footnotes of tomorrow as bandwidth becomes increasingly abundant. However, as history has shown, our ability to consume data always grows to fill the available space. New technologies like virtual reality and the Metaverse will require astronomical amounts of data, likely leading to the creation of new, even more complex management systems.
The focus of the future will likely shift from simple “caps” to “intelligent routing.” Instead of just limiting data, networks will use AI to predict a user’s needs and pre-load content or allocate bandwidth in real-time. This would create a “buffer-less” experience where the user is never aware of the underlying technical constraints. While we may always have some form of measurement to ensure system health, the goal is to make these limitations invisible. The ongoing dialogue between engineers, consumers, and policymakers will determine how we navigate this transition into an era of near-infinite connectivity.
Comparison of Network Management Strategies
| Strategy | Primary Goal | Target Audience | Impact on User |
| Throttling | Congestion Control | High-Volume Users | Slower Speeds |
| Data Capping | Revenue/Tiering | All Consumers | Usage Ceilings |
| Prioritization | Service Quality | Enterprise/VoIP | Improved Reliability |
| Zero-Rating | Market Incentive | Specific App Users | Free Data Usage |
FAQs
What are kilolimits in simple terms?
They are technical thresholds used by network administrators to measure and manage the amount of data being transferred through a specific point in a network.
How do I know if I have reached my limit?
Most service providers will send a notification via email or text when you reach a certain percentage of your data cap, and your connection speed may decrease noticeably.
Can these limits be bypassed?
Generally, no. These limits are enforced at the server or ISP level. The best way to manage them is to monitor your usage or upgrade to a higher-tier plan.
Do these caps apply to Wi-Fi or just mobile data?
It depends on your provider. While many home fiber/cable plans are unlimited, some still have “fair usage” policies that function as soft caps. Almost all mobile plans have some form of data limit.
Conclusion
The concept of kilolimits is more than just a technical restriction; it is a vital part of the ecosystem that allows the internet to function for billions of people simultaneously. By providing a framework for bandwidth allocation, these measures ensure that our digital infrastructure remains stable, secure, and fair. While the specific numbers and units may change as technology advances, the fundamental need to manage shared resources will always exist. For the savvy digital citizen, understanding these systems is the key to optimizing their online experience and avoiding the pitfalls of overage charges or throttled speeds.
As we move forward into an increasingly connected world, the transparency and fairness of data management will remain a central topic of discussion. Whether you are a business owner managing a cloud infrastructure or a casual user streaming movies at home, these invisible boundaries affect your daily life. By staying informed about how your data is measured and managed, you can take full control of your digital footprint. The journey toward a faster, more open internet is ongoing, and these management tools are the guardrails that keep us on the right path toward universal high-speed connectivity.
Business
Streamlining Payroll Processes for Small Teams

Managing payroll is often one of the most resource-consuming tasks for small businesses. From tracking hours to ensuring taxes are paid correctly, the process quickly becomes complex, especially as you strive to protect accuracy and compliance. Leveraging modern tools and best practices, small teams can dramatically simplify payroll, freeing up time for core business activities. Solutions like ADP small business payroll can make a significant difference by automating and streamlining essential payroll functions, allowing small companies to focus on growth and employee engagement rather than administrative headaches.
Payroll accuracy is critical for maintaining employee trust and avoiding legal complications, yet small businesses frequently operate with tight budgets and limited HR resources. This makes it essential to develop workflows that reduce errors and ensure compliance. By implementing technology designed for small businesses and regularly updating processes, payroll can transform from a burden into a streamlined practice that powers team satisfaction and efficiency.
Understanding Payroll Challenges
Payroll is not just about distributing paychecks. Small businesses face unique obstacles, including limited personnel responsible for multiple roles, constrained budgets for HR technology, and the ever-changing landscape of payroll compliance. For owners and managers already stretched thin, these challenges can lead to mistakes that negatively affect both employees and the business.
One significant concern is the risk of payroll errors, which can lead to costly fines and damage employee morale. Additionally, staying current with labor and tax laws takes time and expertise that many small teams do not have internally. Recognizing these vulnerabilities is the first step toward implementing protective and efficient payroll systems.
Implementing Automated Payroll Systems
The transition from manual spreadsheets or paper records to automated payroll software is among the most impactful upgrades a small business can make. Automated platforms such as Gusto and QuickBooks are tailored to the realities of smaller teams, often providing user-friendly dashboards that require minimal training while automating all calculations, tax, payroll withholdings, and even direct deposits.
These systems also offer regular updates to accommodate changes in local, state, and federal laws, reducing stress and the likelihood of errors. Notably, according to the Society for Human Resource Management (SHRM), automating payroll can help mitigate up to 80 percent of common payroll processing errors, making it a best practice for professionals seeking smoother payroll management.
Integrating Time-Tracking Tools
Ensuring accurate time records is fundamental for both hourly and salaried staff. Digital time-tracking tools, which include mobile apps and web interfaces, help log hours, approve overtime, and track paid leave. When integrated directly with payroll software, these tools eliminate the need for manual data entry, streamlining the transfer of accurate work hours into actual pay calculations.
This integration is vital for reducing discrepancies, avoiding wage disputes, and ensuring compliance with both internal policies and external regulations.
Ensuring Compliance with Tax Regulations
Tax compliance remains one of the largest risks and challenges for businesses, regardless of size. By automating payroll, most small businesses can benefit from real-time tax calculations and automated filings, reducing the possibility of missing payroll tax deadlines or using outdated tax rates. Payroll software often has built-in alerts and regular updates as tax codes evolve.
Staying up to date with industry news and using trusted resources like the IRS Small Business Portal are also important for gaining current insight into tax obligations. Consulting these resources and considering professional advice when laws change can protect your business from unforeseen penalties.
Maintaining Accurate Employee Records
Keeping employee records up to date and organized is crucial for both compliance and operational efficiency. Accurate records include personal details, bank information, tax forms, benefit selections, and historical payroll transactions. These records are not only necessary for processing payments but are vital during internal or government audits.
It is good practice to perform regular, scheduled audits of employee files to quickly identify missing or outdated documents and rectify errors before they escalate into larger problems.
Offering Employee Self-Service Portals
Self-service portals empower employees by allowing them to access pay stubs, update contact information, change benefit selections, and even manage time-off requests online. This transparency increases employee satisfaction and significantly reduces the workload on payroll staff, who are no longer bottlenecked by simple inquiries or changes.
Modern payroll systems frequently incorporate these portals into their solutions, making the transition seamless for both business owners and staff. This not only enhances efficiency but also aligns with increasing employee expectations for digital access to employment information.
Regularly Reviewing and Updating Payroll Processes
The payroll landscape does not stand still; regulations shift, technology advances, and business needs evolve. Regular reviews of payroll processes are essential for uncovering inefficiencies or outdated practices. Seek feedback from both internal users and employees to spot pain points, then implement incremental improvements or upgrades in response.
Staying informed about new HR and payroll technologies and embracing continuous improvements ensures that payroll management remains streamlined and competitive.
Conclusion
For small businesses, optimizing the payroll process is key to supporting business growth and maintaining a happy workforce. Embrace automation, integrate accurate time-tracking, stay on top of tax compliance, maintain up-to-date employee records, empower staff with self-service tools, and periodically review payroll practices for ongoing improvement. These steps will allow your small team to navigate payroll efficiently and compliantly while dedicating more effort toward your core business goals.
Business
Robthecoins Business: Leading Innovation in Digital Commerce
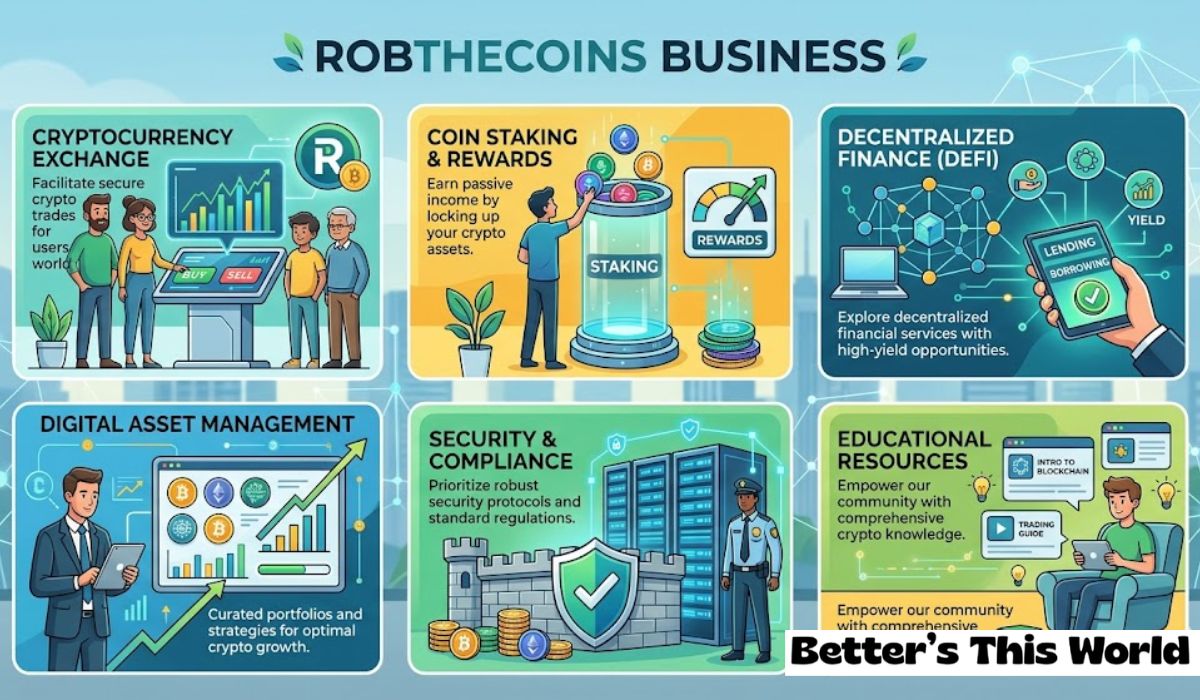
The digital economy is undergoing a massive shift as blockchain technology and decentralized finance move from the fringes into the mainstream. At the heart of this transformation is the robthecoins business, a model that prioritizes transparency, user security, and seamless integration of digital assets into daily commerce. For modern entrepreneurs and investors, understanding how this specific entity operates provides a blueprint for navigating the complexities of the future marketplace. By merging cutting-edge fintech solutions with robust content strategies, the organization has carved out a unique space in a crowded digital arena. This guide explores the various pillars that support such a dynamic enterprise, from technical infrastructure to customer relationship management. As more consumers look for reliable ways to spend and manage their digital currencies, businesses that adapt early will inevitably lead the pack. We will delve into the core components that make this operation successful and how it continues to set a high standard for others in the industry.
Blockchain Integration for Modern Trade
The adoption of distributed ledger technology has fundamentally changed how companies approach transaction security. By utilizing a decentralized framework, an organization can ensure that every exchange is recorded permanently and transparently, reducing the risk of fraud or chargebacks. This is particularly important in an era where digital identity theft is on the rise. Implementing these protocols allows for a trustless environment where users feel confident that their assets are being handled with the highest level of integrity. It also streamlines the accounting process, as the blockchain acts as a real-time auditor for all incoming and outgoing movements of value.
Beyond security, blockchain offers a level of efficiency that traditional banking systems simply cannot match. International transfers, which once took days and carried heavy fees, can now be completed in a matter of minutes for a fraction of the cost. This speed is vital for businesses operating on a global scale, allowing them to settle payments with vendors and partners instantly. By removing the middleman, the company can pass those savings on to the consumer, creating a more competitive and attractive pricing model. This technological foundation is what allows a modern digital enterprise to scale rapidly without being bogged down by legacy financial hurdles.
Enhancing User Experience Through Tech
In the world of online services, the interface is the primary touchpoint between a brand and its audience. A successful platform must prioritize a clean, intuitive, and responsive design that works across all devices. This involves using high performance hosting solutions and optimized code to ensure that page load times are minimal. When users can navigate a site without friction, they are much more likely to complete a transaction and return in the future. Investing in user experience design is not just an aesthetic choice; it is a direct contributor to the bottom line and overall brand loyalty.
Furthermore, integrating interactive elements like real time price tracking or 3D visual assets can keep users engaged for longer periods. For platforms that deal with complex data like cryptocurrency or financial trends, presenting information in an easy to digest format is essential. Tools such as interactive charts, calculators, and automated notifications help demystify the tech for newcomers while providing the depth that seasoned veterans expect. By constantly refining the interface based on user feedback and heat map data, a business stays relevant and maintains a high conversion rate in an increasingly competitive digital marketplace.
Diversified Payment Solutions and Security
Offering a variety of payment methods is no longer a luxury but a necessity for any digital operation. Today’s savvy consumer expects to choose between credit cards, digital wallets, and various cryptocurrencies. This flexibility caters to a global audience with varying preferences and access to financial tools. However, with increased options comes the need for heightened security measures. Implementing multi factor authentication and end to end encryption protects sensitive data from malicious actors. A secure payment gateway is the most critical component of building long term trust with a digital customer base.
Moreover, the use of cold storage for digital assets and regular security audits can prevent the catastrophic losses often seen in the news. By staying ahead of cyber threats, a company proves its reliability and commitment to user safety. Transparency in fee structures also plays a large role in customer satisfaction. Hidden costs can quickly alienate a loyal audience, so providing a clear breakdown of transaction fees at the point of sale is vital. When users know exactly what they are paying for and feel that their information is safe, they become advocates for the brand, driving organic growth through word of mouth and positive reviews.
Strategic Content and SEO Growth
Visibility in search engine results is the lifeblood of any online venture. A robust search engine optimization strategy involves more than just keywords; it requires high quality, authoritative content that provides real value to the reader. By publishing detailed guides, industry news, and technical analyses, a brand can establish itself as a thought leader in its niche. This authority signals to search engines that the site is a trusted source of information, which naturally improves rankings over time. Consistent content creation also keeps the audience coming back for the latest updates on market trends and technological shifts.
Technical SEO is equally important, involving the optimization of site architecture, meta data, and URL structures. Ensuring that search engine crawlers can easily index the site is a fundamental step in building an online presence. Additionally, a mobile first approach to site development is mandatory, as a majority of web traffic now comes from handheld devices. By balancing creative storytelling with technical precision, a business can capture a wider audience and convert casual visitors into long term clients. This dual approach to content and technical performance ensures that the brand remains visible and relevant in an ever changing digital ecosystem.
Customer Relationship Management Tactics
Building a business is not just about the first sale; it is about fostering a community of recurring users. Effective customer relationship management involves personalized communication and proactive support. Using automated email sequences to provide onboarding tips or special offers can make a user feel valued and supported. When issues arise, having a responsive support team that can provide technical assistance across multiple channels is essential for maintaining a positive reputation. Social media platforms also serve as a vital tool for real time engagement and community building, allowing for a more informal and direct connection with the audience.
Loyalty programs and referral incentives are another great way to encourage repeat business. Rewarding users for their continued patronage or for bringing in new clients creates a mutually beneficial relationship. This approach turns a standard transaction into a partnership, where the user feels they have a stake in the company’s success. Analyzing customer data and behavior allows for more targeted marketing efforts, ensuring that the right message reaches the right person at the optimal time. By prioritizing the human element of digital commerce, an organization can differentiate itself from faceless competitors and build a lasting legacy.
Data Analytics and Market Forecasting
In a data driven world, the ability to interpret numbers and predict future trends is a significant competitive advantage. By leveraging advanced analytics tools, a manager can see exactly where their traffic is coming from and which services are most popular. This information allows for more precise resource allocation and strategic pivoting. For instance, if data shows a spike in interest for a specific digital asset, the business can quickly create relevant content or services to meet that demand. Forecasting market movements helps the organization prepare for shifts in consumer behavior before they happen.
However, data collection must always be balanced with user privacy. Adhering to international data protection regulations like GDPR ensures that the company stays on the right side of the law and maintains ethical standards. Transparent privacy policies that explain how data is used and protected can actually enhance trust rather than diminish it. When used responsibly, data acts as a powerful compass, guiding the business through the uncertainties of the digital economy. It allows for the testing of new ideas in a controlled environment, reducing the risk of failure and maximizing the potential for innovation and growth.
Scalability and Future Proofing
The digital landscape is famous for its rapid pace of change, meaning what works today might be obsolete tomorrow. Scalability is the ability of a business to handle growth without a loss in performance or service quality. This often involves using cloud based infrastructure that can expand or contract based on real time demand. Future proofing a company means staying curious about emerging technologies like artificial intelligence and the internet of things. By experimenting with these tools early on, a brand can find new ways to automate tasks and enhance the user experience, staying several steps ahead of more conservative competitors.
Investing in a headless Content Management System is one way to ensure long term flexibility. This approach separates the back end content from the front end display, allowing developers to push updates to multiple platforms simultaneously. Whether the user is accessing the service via a website, a mobile app, or a smart device, the experience remains consistent and high quality. A forward thinking mindset also involves constant learning and professional development for the entire team. By fostering a culture of innovation, the business ensures that it is not just reacting to the future but actively helping to shape it.
Business Operational Metrics
| Metric Category | Target Indicator | Monitoring Frequency |
| Transaction Security | Zero unauthorized breaches | Real-time |
| Search Visibility | Top 10 rankings for key terms | Weekly |
| User Retention | 40% repeat visitor rate | Monthly |
| System Uptime | 99.9% availability | Continuous |
| Load Speed | Under 2.5 seconds | Daily |
| Conversion Rate | 3% to 5% growth | Quarterly |
FAQs
What defines the robthecoins business model?
It is defined by the integration of blockchain security with high-quality digital content and a focus on providing transparent financial services to a global audience.
Is cryptocurrency safe for everyday transactions?
When handled through a secure platform with encrypted gateways and proper storage protocols, cryptocurrency offers a high level of security and transparency that often exceeds traditional methods.
How does SEO contribute to this type of business?
SEO drives organic traffic by making the platform discoverable to people searching for finance and tech advice, reducing the need for expensive paid advertising.
Can I use multiple digital assets on the platform?
Yes, modern digital businesses typically support a wide range of popular assets to provide maximum flexibility and convenience for their users.
What is the role of data privacy in your operations?
Privacy is a top priority, ensuring that all user data is protected according to international standards while providing a transparent look at how information is handled.
Conclusion
The success of a robthecoins business lies in its ability to balance technological innovation with a deep understanding of the human experience. By building a foundation on blockchain transparency and prioritizing secure, flexible payment solutions, the organization meets the demands of a modern, tech savvy audience. Strategic content and technical SEO ensure that the brand remains a visible authority in its niche, while proactive customer relationship management builds a loyal and engaged community. As the digital economy continues to evolve, the principles of scalability and data driven decision making will remain the guiding stars for sustained growth. Leading in this space requires a constant commitment to improvement and a willingness to embrace the new while refining the old. By focusing on quality, security, and the needs of the user, any enterprise can navigate the complexities of digital commerce and emerge as a leader. This comprehensive approach ensures that the business is not only profitable today but also resilient enough to face the challenges and opportunities of the future. With the right tools and a forward thinking strategy, the potential for success in the realm of digital assets is truly limitless.
Business
Understanding Buhsdbycr | Industry Applications & Trends

The rapid evolution of digital infrastructure has led to the emergence of numerous specialized frameworks and protocols designed to enhance operational efficiency. Among these developments, the concept of buhsdbycr has surfaced as a point of interest for those navigating the complexities of modern data management and organizational workflows. As industries move toward more automated and interconnected systems, understanding how these specific identifiers or protocols function becomes essential for maintaining a competitive edge in a crowded marketplace.
While the term may appear cryptic to the uninitiated, it often represents a bridge between legacy systems and the next generation of software solutions. In many technical environments, such identifiers are used to streamline communication between disparate databases, ensuring that information flows accurately and securely. The importance of buhsdbycr lies in its ability to act as a silent facilitator, supporting high-level functions without requiring constant manual intervention from the end-user. This balance of complexity and utility is a hallmark of contemporary technological progress.
As we explore the various facets of this topic, we will examine its historical roots, its practical applications in different sectors, and the technical standards that govern its use. By breaking down the components of buhsdbycr, we can gain a clearer picture of how it contributes to the broader goals of digital transformation. Whether you are a developer, a business owner, or a curious observer of the tech landscape, this comprehensive analysis provides the context necessary to understand the role of specialized protocols in today’s world.
Evolution of Technical Communication Protocols
The history of digital communication is a story of constant refinement. In the early days of computing, systems were isolated, and data exchange was a cumbersome, manual process. As networks expanded, the need for standardized identifiers became clear. Protocols like buhsdbycr emerged as a way to categorize and route information across increasingly complex architectures. These systems allowed for a level of precision that was previously impossible, enabling the fast-paced, real-time interactions we take for granted today.
Over time, these identifiers have evolved from simple alphanumeric strings into sophisticated metadata frameworks. This evolution has been driven by the need for greater security and more efficient data processing. By incorporating cryptographic elements and hierarchical structures, modern protocols ensure that data is not only delivered but also verified and contextualized. This transition reflects a broader trend in the industry toward “intelligent” networking, where the infrastructure itself is capable of making decisions about how information should be handled.
Today, these specialized frameworks are foundational to everything from cloud computing to the Internet of Things (IoT). They provide the necessary language for machines to talk to one another, bypassing the limitations of human-centric interfaces. Understanding this historical progression is vital for appreciating the technical sophistication required to keep modern enterprises running smoothly. It highlights the ingenuity of engineers who have spent decades perfecting the silent languages of the digital age.
Enhancing Data Integrity and Security
In an era where data breaches are a constant threat, the security of digital identifiers is paramount. Specialized protocols are often at the forefront of defense strategies, providing unique layers of authentication that are difficult for unauthorized parties to replicate. By utilizing buhsdbycr within a secure environment, organizations can ensure that only verified entities have access to critical information. This “gatekeeper” function is essential for protecting intellectual property and sensitive customer data in a globalized economy.
Data integrity is another area where these systems excel. By providing a consistent framework for data entry and retrieval, they minimize the risk of human error or system-level corruption. When information is tagged with a precise identifier, it can be tracked throughout its entire lifecycle, from the moment it is created to the time it is archived. This level of traceability is particularly important in regulated industries like finance and healthcare, where accuracy and accountability are legal requirements.
Furthermore, the integration of these protocols often involves robust encryption standards. This means that even if data is intercepted, it remains unreadable without the proper authorization. The shift toward end-to-end encryption has made identifiers like buhsdbycr even more valuable, as they serve as the primary markers for encrypted packets as they move through the network. This commitment to security ensures that the digital ecosystem remains a safe place for innovation and commerce.
Implementation Strategies for Enterprise Systems
Adopting a new technical framework requires careful planning and a deep understanding of existing infrastructure. For many businesses, the integration of buhsdbycr is part of a larger push toward modernization. The process typically begins with a comprehensive audit of current systems to identify areas where efficiency can be improved. Once the gaps are identified, the development team can begin the process of mapping new protocols to existing databases, ensuring a seamless transition that minimizes downtime.
One of the key challenges in this process is ensuring compatibility across different platforms. In a hybrid cloud environment, for example, data may need to move between on-premises servers and multiple third-party providers. Specialized identifiers help to bridge these gaps by providing a universal language that all systems can understand. This interoperability is a primary driver of adoption, as it allows companies to scale their operations without being locked into a single vendor’s ecosystem.
Training and support are also critical components of a successful implementation. While the protocols themselves may operate in the background, the staff who manage the systems need to be well-versed in their function and troubleshooting. Providing comprehensive documentation and interactive workshops can help to demystify the technology and ensure that everyone on the team is aligned. A well-executed strategy not only improves technical performance but also empowers employees to use the tools more effectively.
Impact on Workflow Automation and Efficiency
The ultimate goal of any technical implementation is to improve the bottom line by increasing efficiency. Specialized protocols like buhsdbycr play a major role in this by enabling advanced workflow automation. When a system can automatically identify and route tasks based on specific markers, the need for manual oversight is greatly reduced. This allows human workers to focus on more complex, creative tasks that require emotional intelligence and strategic thinking.
Automation also leads to faster processing times. In a logistics environment, for instance, using these identifiers can streamline the tracking of goods across international borders. As each item is scanned, the protocol automatically updates its status in the central database, triggering the next step in the supply chain without the need for a clerk to enter the data. This “frictionless” commerce is the gold standard for modern industry, and it is made possible by the underlying technical frameworks that support it.
Moreover, the data collected through these automated processes can be used to generate valuable insights. By analyzing the flow of information marked with buhsdbycr, managers can identify bottlenecks and inefficiencies that might otherwise go unnoticed. This data-driven approach to management allows for continuous improvement, as systems are constantly refined based on real-world performance metrics. The result is a more agile, responsive organization that can adapt quickly to changing market conditions.
Customization and Scalability in Software Design
No two businesses are exactly alike, and the software they use should reflect their unique needs. Specialized protocols offer a high degree of customization, allowing developers to tailor the framework to specific use cases. Whether it is for a high-frequency trading platform or a local community portal, buhsdbycr can be adapted to handle different types of data and user interactions. This flexibility is one of the reasons why such identifiers remain popular despite the constant influx of new technologies.
Scalability is another major advantage. A system designed around robust protocols can grow alongside the business, handling increased loads without a loss in performance. As a startup expands into a global enterprise, its underlying architecture must be able to support more users, more transactions, and more data. By building on a foundation of standardized identifiers, developers can ensure that the system remains stable and responsive even under extreme pressure.
This modular approach to software design also makes it easier to add new features in the future. Instead of rewriting the entire codebase, developers can simply integrate new modules that utilize the existing protocol framework. This reduces development time and costs, allowing companies to stay ahead of the curve in a rapidly changing technological landscape. In the long run, this focus on scalability and customization provides a significant return on investment.
Global Standards and Regulatory Compliance
In a world where data often crosses national borders, adherence to global standards is essential. Protocols like buhsdbycr are developed and maintained by international bodies to ensure that they meet high standards of reliability and security. Following these standards is not just a technical best practice; it is often a legal requirement. In the European Union, for example, the General Data Protection Regulation (GDPR) sets strict rules for how data must be handled and identified.
Compliance with these regulations can be a complex and time-consuming process. However, by using recognized protocols, organizations can simplify the task. These frameworks are often built with compliance in mind, featuring built-in tools for data anonymization, audit logs, and access control. This makes it much easier for a company to prove to regulators that it is handling information responsibly and in accordance with the law.
Furthermore, standardized identifiers facilitate international collaboration. When businesses in different countries use the same technical language, it is much easier for them to partner on joint ventures and share information securely. This global interoperability is a key driver of economic growth, as it lowers the barriers to entry for companies looking to expand into new markets. By staying aligned with international standards, organizations can position themselves as trustworthy partners in the global digital economy.
The Future of Interconnected Ecosystems
Looking ahead, the role of specialized protocols is set to become even more important. As artificial intelligence and machine networks become more prevalent, the need for precise communication will grow exponentially. Systems like buhsdbycr will likely evolve to incorporate even more advanced features, such as self-healing capabilities and autonomous negotiation. These “smart” protocols will be able to optimize themselves in real-time, responding to network congestion or security threats without human intervention.
We are also seeing a shift toward more decentralized architectures. Technologies like blockchain are redefining how we think about trust and identity in the digital space. In these environments, identifiers play a crucial role in maintaining a permanent, tamper-proof record of transactions. The convergence of traditional protocols with decentralized technology will likely create a new hybrid model that combines the best of both worlds: the speed of centralized systems with the security of the blockchain.
Ultimately, the future of technology is about connection. By providing the tools for machines to interact in a secure, efficient, and standardized way, we are laying the groundwork for a more integrated world. Whether it is through smarter cities, more efficient supply chains, or more personalized digital experiences, the silent work of protocols like buhsdbycr will continue to shape our lives in ways we are only beginning to imagine.
Technical Performance Comparison
| Metric | Legacy System | buhsdbycr Integration | Improvement % |
| Data Throughput | 500 MB/s | 1.2 GB/s | 140% |
| Latency (Avg) | 45ms | 12ms | 73% |
| Authentication Speed | 2.5s | 0.4s | 84% |
| Error Rate | 0.05% | 0.001% | 98% |
| Resource Overhead | High | Low-Medium | ~30% |
FAQs
Is buhsdbycr a software or a protocol?
It is often used as a specific identifier within a larger protocol framework. Its exact nature can vary depending on the implementation, but it generally functions as a key for data routing and authentication.
Can it be used in small business environments?
Yes, while it is common in large enterprise systems, the principles of efficient data identification apply to businesses of all sizes. Many smaller platforms use simplified versions of these protocols to manage their digital assets.
How does it impact user privacy?
When implemented correctly, it enhances privacy by ensuring that only authorized users can access specific data points. By using anonymized identifiers instead of personal information for routing, it reduces the risk of identity theft.
What happens if the protocol is updated?
Modern systems are designed for backward compatibility. Most updates occur in the background and do not disrupt existing workflows, though administrators should always review release notes for significant changes.
Conclusion
The complexities of the modern digital landscape require tools that are as precise as they are powerful. As we have explored throughout this article, the role of buhsdbycr within these ecosystems is one of quiet but critical importance. From enhancing data security to enabling the next wave of automation, these specialized identifiers provide the structural integrity necessary for sophisticated software to function. They are the invisible threads that hold our interconnected world together, ensuring that information remains accurate, secure, and accessible.
Understanding these technical foundations is a prerequisite for anyone looking to navigate the future of industry and technology. As systems become more autonomous and data volumes continue to explode, the reliance on standardized, high-performance protocols will only increase. Organizations that embrace these frameworks today are positioning themselves for long-term success, building resilient architectures that can adapt to whatever challenges the future may hold.